The TLS handshake (Transport Layer Security handshake) is the process by which a client and server establish a secure, encrypted connection before exchanging data. It occurs at the beginning of every HTTPS connection and involves several round-trips: the client sends supported cipher suites, the server responds with its certificate and chosen cipher, the client verifies the certificate, and both parties derive encryption keys.
The TLS handshake adds latency to the first request (typically 1-3 round-trips depending on the TLS version). TLS 1.3 (the latest version) reduces this to a single round-trip, and supports 0-RTT resumption for repeat connections. The handshake time is influenced by network latency, certificate chain length, and the computational cost of the selected cipher.
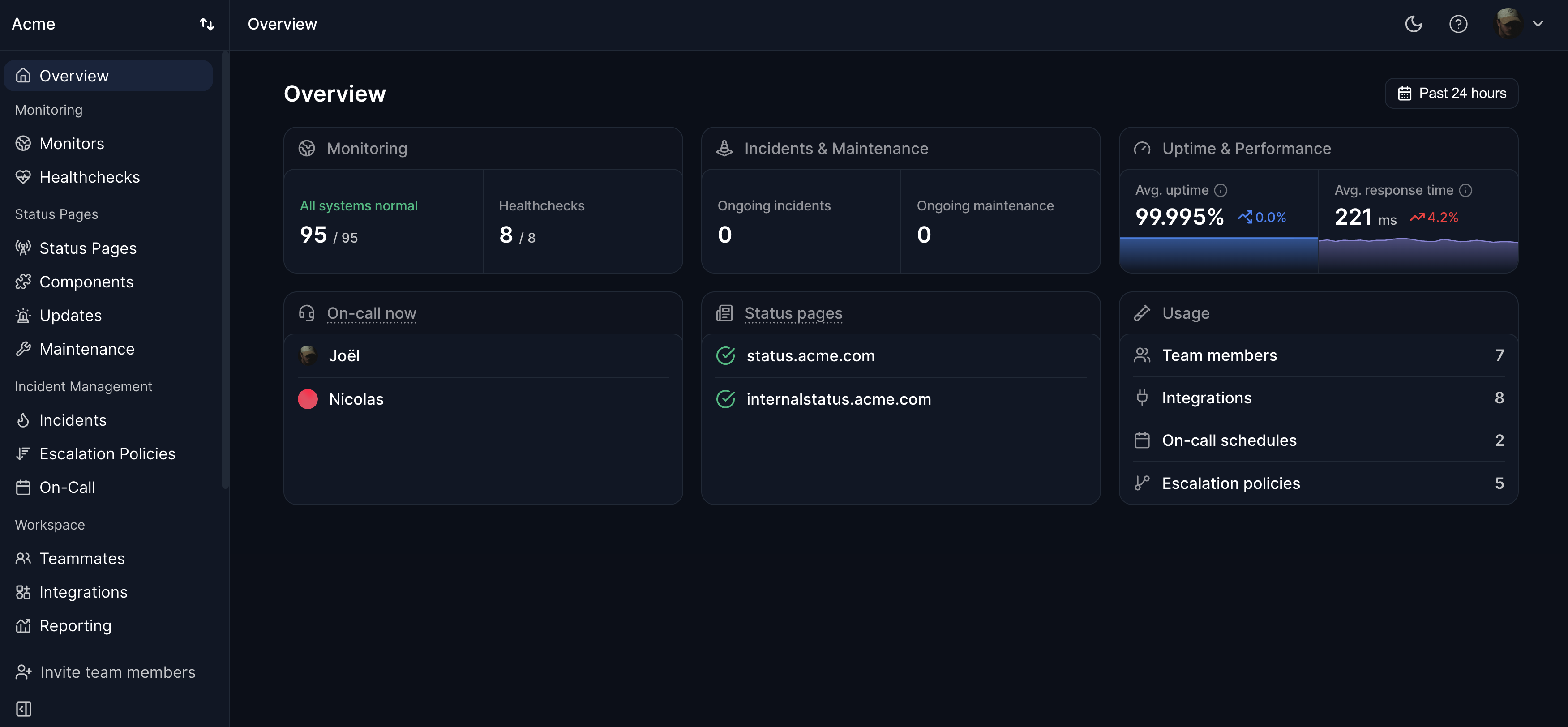
Monitoring TLS handshake time reveals issues like slow certificate revocation checks, oversized certificate chains, or network problems. Abnormally long handshake times degrade user experience even when the server itself is fast. SSL monitoring tools like Hyperping track certificate validity and can detect TLS-related issues that affect connection establishment.